"It's the gravity that shapes the large scale structure of the universe, even though it is the weakest of four categories of forces." -Stephen Hawking
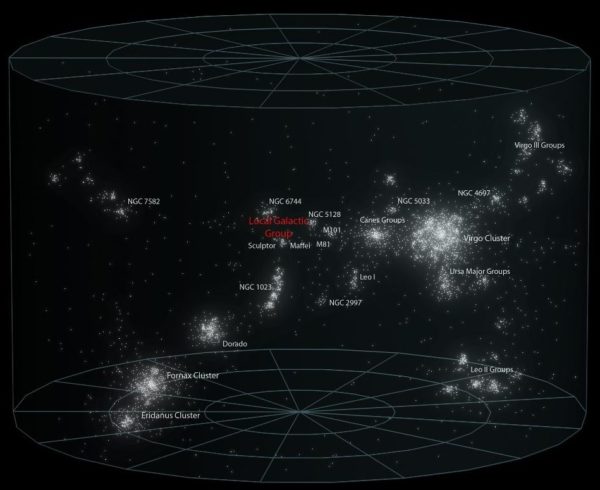
Galaxies don’t just exist in isolation in our Universe, but are often found bound together as a part of even grander structures. Our own Milky Way is bound in a galactic group (our local group), nearby are larger groups and galaxy clusters, and on still larger scales, cosmic superclusters appear to encompass as many as 100,000 individual galaxies.
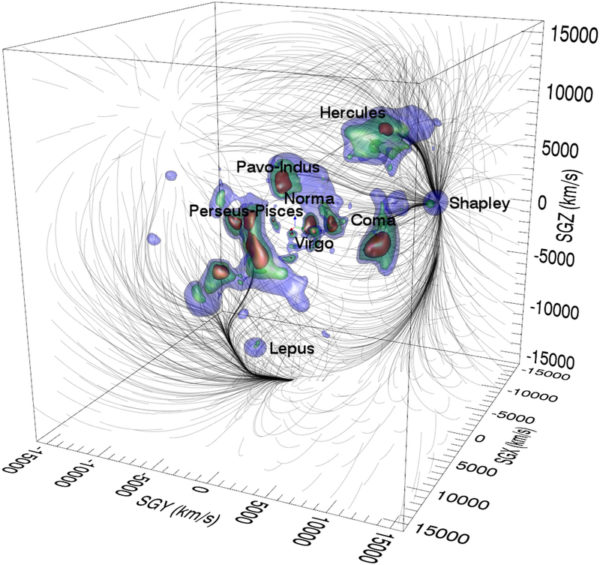 Outlined in light blue, giant collections of galaxies can be divided up into superclusters. But this classification doesn't make superclusters real. Image credit: The Laniakea supercluster of galaxies R. Brent Tully, Hélène Courtois, Yehuda Hoffman & Daniel Pomarède, Nature 513, 71–73 (04 September 2014).
Outlined in light blue, giant collections of galaxies can be divided up into superclusters. But this classification doesn't make superclusters real. Image credit: The Laniakea supercluster of galaxies R. Brent Tully, Hélène Courtois, Yehuda Hoffman & Daniel Pomarède, Nature 513, 71–73 (04 September 2014).
Yet it isn’t sufficient to simply see what appears to be a collection and draw an imaginary line around it. You can’t just give something a name and proclaim that it’s meaningful because you defined it. Instead, for a collection of objects in space, they need to be gravitationally bound together and connected. Thanks to dark energy, these superclusters aren’t.

IMHO I don't think we can really say Cosmic superclusters do not actually exist. By looking at Laniakea in the image, it clearly has a structure/order. It just does not have "gravitationally bound" property that smaller clusters have.
There are countless similar situations in math for example. (Probably many in physics also.)
What I mean is nobody considers fifth degree and above polynomials are not polynomials because they don't have full solutions like polynomials of degrees up to four.
Nobody considers quaternions an invalid number system because they don't have some properties of real or complex numbers. Octonions and Sedenions don't have even more properties. But they are still accepted as valid number systems of higher dimensions.
I think an example from astronomy is neutron stars. They are still stars but only w/o some properties of regular stars.
They are not made of plasma; their centers do not do nuclear fusion etc.
Frank, "they are superclusters" may be no more real than the sheep up in the sky. Our minds are set to look for regularities and then latch on to them. There may be no actual regularities, just the happenstance.
See also the paintings done by an elephant. They may sell as art, but what people see in it isn't what the elephant put there, just what their own minds did.
@Frank#1: All polynomials, even those of degree higher than four, do have full solutions. The fundamental theorem of algebra sees to that. You must mean solutions in radicals, but there really is nothing special about radicals. More general functions known as Siegel modular functions (By the way, Ethan, do you have any relation to Carl Ludwig Siegel?) and hyperelliptic integrals have been developed to express the solutions to polynomial equations of arbitrarily high degree (Thomae’s formula).
Your other examples are of mathematical structures, which are explicitly defined to follow certain axioms, which of course makes them legitimate. Galactic clusters however, don’t have any inherent property to them. They aren’t gravitationally bound, and they appear to have structure by happenstance only. They are just as real as people seeing the face of Jesus in a tortilla.
Sounds rather like a case of semantics. The parts may not be tied together but have a relative similar origin, thinking here of solething like a cluster bomb.
On the orher hand a cluster could be formed due to an external factor like for a Voronoi pattern, fields clashing and it is the opposite of the cluster bomb.
Besides of common origin, Super Clusters could be also bonded thru filaments of Dark Matter (if exists).
I think that saying that cosmic superclusters don't exist might be a bit general. When I think of cluster I think something bunched together, I think some parts might move away, but generally its a clump or cluster. It still exists/ed. I do however agree its crazy to see a clump, name it, and draw a circle around it, because as you said, dark energy and matter create movement.
I think it's very interesting and needs to be more researched the idea of dark energy. I read some about it here (https://science.nasa.gov/astrophysics/focus-areas/what-is-dark-energy) It offers various theories about dark energy.